Cyber attacks give another option — less devastating than a nuclear attack, but capable of giving a country a strategic and psychological edge
Washington: Early last summer, Chinese and Indian troops clashed in a surprise border battle in the remote Galwan Valley, bashing each other to death with rocks and clubs.
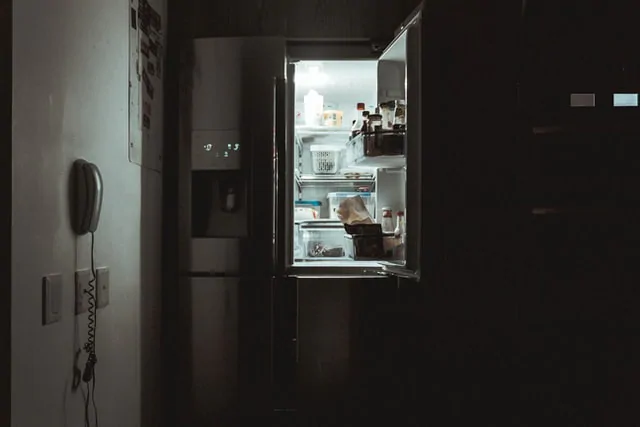
Four months later and more than 1,500 miles away in Mumbai, trains shut down and the stock market closed as the power went out in a city of 20 million people. Hospitals had to switch to emergency generators to keep ventilators running amid a coronavirus outbreak that was among India’s worst.
outbreak that was among India’s worst.
Now, a new study lends weight to the idea that those two events may have been connected — as part of a broad Chinese cyber campaign against India’s power grid, timed to send a message that if India pressed its claims too hard, the lights could go out across the country.
The study shows that as the battles raged in the Himalayas, taking at least two dozen lives, Chinese malware was flowing into the control systems that manage electric supply across India, along with a high-voltage transmission substation and a coal-fired power plant.
The flow of malware was pieced together by Recorded Future, a Somerville, Massachusetts, company that studies the use of the internet by state actors. It found that most of the malware was never activated. And because Recorded Future could not get inside India’s power systems, it could not examine the details of the code itself, which was placed in strategic power-distribution systems across the country. While it has notified Indian authorities, so far they are not reporting what they have found.
Stuart Solomon, Recorded Future’s chief operating officer, said that the Chinese state-sponsored group, which the firm named Red Echo, “has been seen to systematically utilise advanced cyber intrusion techniques to quietly gain a foothold in nearly a dozen critical nodes across the Indian power generation and transmission infrastructure.”
The discovery raises the question about whether an outage that struck on 13 October in Mumbai was meant as a message from Beijing about what might happen if India pushed its border claims too vigorously.
News reports at the time quoted Indian officials as saying that the cause was a Chinese-origin cyber attack on a nearby electricity load-management centre. Authorities began a formal investigation, which is due to report in the coming weeks. Since then, Indian officials have gone silent about the Chinese code, whether it set off the Mumbai blackout and the evidence provided to them by Recorded Future that many elements of the nation’s electric grid were the target of a sophisticated Chinese hacking effort.
It is possible the Indians are still searching for the code. But acknowledging its insertion, one former Indian diplomat noted, could complicate the diplomacy in recent days between Indian foreign minister S Jaishankar and his Chinese counterpart, Wang Yi, in an effort to ease the border tensions.
The investigators who wrote the Recorded Future study, which is set to be published on Monday, said that “the alleged link between the outage and the discovery of the unspecified malware” in the system “remains unsubstantiated.” But they noted that “additional evidence suggested the coordinated targeting of the Indian load dispatch centres,” which balance the electrical demands across regions of the country.
The discovery is the latest example of how the conspicuous placement of malware in an adversary’s electric grid or other critical infrastructure has become the newest form of both aggression and deterrence — a warning that if things are pushed too far, millions could suffer.
“I think the signalling is being done” by China to indicate “that we can and we have the capability to do this in times of a crisis,” said retired Lieutenant-General. DS Hooda, a cyber expert who oversaw India’s borders with Pakistan and China. “It’s like sending a warning to India that this capability exists with us.”
Both India and China maintain medium-size nuclear arsenals, which have traditionally been seen as the ultimate deterrent. But neither side believes that the other would risk a nuclear exchange in response to bloody disputes over the Line of Actual Control, an ill-defined border demarcation where long-running disputes have escalated into deadly conflicts by increasingly nationalistic governments.
Cyber attacks give them another option — less devastating than a nuclear attack, but capable of giving a country a strategic and psychological edge. Russia was a pioneer in using this technique when it turned the power off twice in Ukraine several years ago.
And the United States has engaged in similar signaling. After the Department of Homeland Security announced publicly that the American power grid was littered with code inserted by Russian hackers, the United States put code into Russia’s grid in a warning to President Vladimir Putin.
Now the Biden administration is promising that within weeks it will respond to another intrusion — it will not yet call it an attack — from Russia, one that penetrated at least nine government agencies and more than 100 corporations.
So far, the evidence suggests that the SolarWinds hack, named for the company that made network-management software that was hijacked to insert the code, was chiefly about stealing information. But it also created the capability for far more destructive attacks — and among the companies that downloaded the Russian code were several American utilities. They maintain that the incursions were managed, and that there was no risk to their operations.
Until recent years, China’s focus had been on information theft. But Beijing has been increasingly active in placing code into infrastructure systems, knowing that when it is discovered, the fear of an attack can be as powerful a tool as an attack itself.
In the Indian case, Recorded Future sent its findings to India’s Computer Emergency Response Team, or CERT-In, a kind of investigative and early-warning agency most nations maintain to keep track of threats to critical infrastructure. Twice the centre has acknowledged receipt of the information, but said nothing about whether it, too, found the code in the electric grid.
Repeated efforts by The New York Times to seek comment from the centre and several of its officials over the past two weeks yielded no response.
The Chinese government, which did not respond to questions about the code in the Indian grid, could argue that India started the cyber aggression. In India, a patchwork of state-backed hackers were caught using coronavirus -themed phishing emails to target Chinese organisations in Wuhan last February. A Chinese security company, 360 Security Technology, accused State-backed Indian hackers of targeting hospitals and medical research organisations with phishing emails, in an espionage campaign.
-themed phishing emails to target Chinese organisations in Wuhan last February. A Chinese security company, 360 Security Technology, accused State-backed Indian hackers of targeting hospitals and medical research organisations with phishing emails, in an espionage campaign.
Four months later, as tensions rose between the two countries on the border, Chinese hackers unleashed a swarm of 40,300 hacking attempts on India’s technology and banking infrastructure in just five days. Some of the incursions were so-called denial-of-service attacks that knocked these systems offline; others were phishing attacks, according to the Maharashtra Police.
By December, security experts at the Cyber Peace Foundation, an Indian non-profit organisation that follows hacking efforts, reported a new wave of Chinese attacks, in which hackers sent phishing emails to Indians related to the Indian holidays in October and November. Researchers tied the attacks to domains registered in China’s Guangdong and Henan provinces, to an organisation called Fang Xiao Qing. The aim, the foundation said, was to obtain a beachhead in Indians’ devices, possibly for future attacks.
“One of the intentions seems to be power projection,” said Vineet Kumar, president of the Cyber Peace Foundation.
The foundation has also documented a surge of malware directed at India’s power sector, from petroleum refineries to a nuclear power plant, since last year. Because it is impossible for the foundation or Recorded Future to examine the code, it is unclear whether they are looking at the same attacks, but the timing is the same.
Yet except for the Mumbai blackout, the attacks have not disrupted the provision of energy, officials said.
And even there, officials have gone quiet after initially determining that the code was most likely Chinese. Yashasvi Yadav, a police official in charge of Maharashtra’s cyber-intelligence unit, said authorities found “suspicious activity” that suggested the intervention of a state actor.
But Yadav declined to elaborate, saying the investigation’s full report would be released in early March. Maharashtra minister Nitin Raut was quoted in local reports in November blaming sabotage for the Mumbai outage, but did not respond to questions about the blackout.
Military experts in India have renewed calls for the government of Prime Minister Narendra Modi to replace the Chinese-made hardware for India’s power sector and its critical rail system.
“The issue is we still haven’t been able to get rid of our dependence on foreign hardware and foreign software,” Hooda said.
Indian government authorities have said a review is underway of India’s information technology contracts, including with Chinese companies. But the reality is that ripping out existing infrastructure is expensive and difficult.
David E Sanger and Emily Schmall c.2021 The New York Times Company
Subscribe to Moneycontrol Pro at ₹499 for the first year. Use code PRO499. Limited period offer. *T&C apply